Security
How Filarr protects your data: files encrypted on your disk, KEK/FEK architecture, optional end-to-end encrypted cloud sync.
KEK / FEK Architecture
Filarr uses a two-level key system. Each file is encrypted with its own File Encryption Key (FEK) using AES-256-GCM. All FEKs are themselves encrypted by a Key Encryption Key (KEK), derived from your password via PBKDF2. If one FEK is compromised, only that file is exposed — not the rest of your data.
Your password stays with you
All encryption and decryption happens on your machine. Your password never leaves your device — and neither does your key in its usable form. When cloud sync is enabled, only encrypted blobs are stored on our servers (Cloudflare R2, EU), alongside a copy of your key that is itself encrypted by your password. We cannot read your files — it’s not a policy, it’s a technical fact.
Two-factor authentication (TOTP)
Optional from Settings > Security inside the app. Compatible with any standard TOTP app (Authy, Google Authenticator, 1Password, Bitwarden). At login: password, then a 6-digit code. 8 single-use backup codes are generated at activation so you aren't locked out if you lose your TOTP device.
The TOTP secret is stored server-side (required to verify codes) but grants no access to your files — it only protects the login to your account. Your password remains the only key that unlocks your data encryption.
- TOTP RFC 6238 (SHA-1, 6 digits, 30s period)
- Every standard TOTP app: Authy, Google Authenticator, 1Password, Bitwarden
- 8 single-use backup codes, hashed server-side
- Rate-limited to 10 attempts / 15 min / IP
Threat Model
Since your plaintext data never leaves your machine — and the copy of your key we store is useless without your password — Filarr’s threat model is fundamentally different from a typical cloud service. The main threats are physical access to your device, losing your password, or a password weak enough to be brute-forced if our servers were ever compromised (which is why we strongly recommend a password manager).
- Physical access to deviceProtected by AES-256-GCM encryption
- Password lossRecoverable via recovery phrase only
- Malware on deviceKeys in memory only during use
- Disk theftData unreadable without password
- Brute force attackPBKDF2 with high iterations
- Online account takeoverProtected by optional TOTP 2FA
What this means in real life
Encryption is only useful if it protects you in the situations that actually happen.
Your laptop gets stolen
Your files are encrypted with AES-256-GCM. Without your vault password, they’re unreadable — even with full disk access. The thief gets an encrypted hard drive, not your documents.
A cloud provider gets breached
Filarr only stores encrypted blobs on our servers. Your files are encrypted on your device before upload. Even if our storage is compromised, attackers get unreadable ciphertext — not your files.
A legal request for your data
If Filarr receives a legal request, we can only hand over encrypted blobs — files plus the encrypted copy of your key. Without your password nothing is decryptable, and we never see your password. This isn’t a policy — it’s a technical fact.
You forget your vault password
This is the cost of end-to-end encryption. Your key is protected by a derivative of your password (PBKDF2-SHA-512, 600,000 iterations), and your password is never transmitted to us — if you lose it, we cannot recover your data. We recommend using a password manager and exporting a recovery key from Settings > Security.
What if Filarr gets curious?
We can’t. Your files are encrypted with a random key, itself protected by a key derived from your password using PBKDF2-SHA-512 with 600,000 iterations. We store that key in encrypted form to enable multi-device access, but we never see your password — so we can never unwrap it. Our servers only see random-looking bytes.
Your internet goes down mid-session
Filarr is local-first. Everything works offline — notes, files, graph, canvas. Changes sync automatically when you reconnect. No internet required to access your own files.
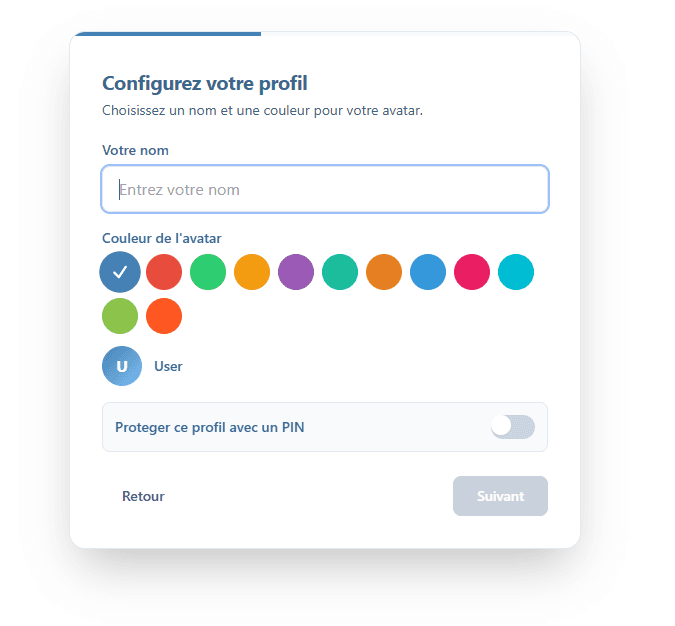
Multi-profile isolation
Each profile in Filarr has its own set of encryption keys. Data in a “Personal” profile is completely isolated from a “Client A” profile. Even if one profile is compromised, the others remain protected.
What we’re still working on
Cloud sync is live with end-to-end encryption — your files are encrypted on your device before upload. The desktop client is now published on GitHub under Business Source License 1.1: you can read the code and verify the cryptographic claims directly, rather than trusting us on our word. An independent security audit is on the roadmap. There’s no SOC2 or HIPAA certification yet.
Same guarantee for file sharing
Filarr Send applies the same AES-256-GCM encryption. The key stays in the URL, never on our servers.